UPDATE: As of 320pm on 1/4, all of the computer lab switches were successfully upgraded.
ITS will be conducting network maintenance in the computer labs in RLC and Miguel Hall on Wednesday, January 4th, which will cause some localized network outages between 1pm and 4pm.
In order to improve the network reliability, there will be scheduled network maintenance in order to replace some old and outdated network equipment. This network maintenance will affect only the wired network in the following computer labs:
RLC Building Room 103 and 105 - from 1pm to 2pm
RLC Building Room 309 - from 2pm to 3pm
Miguel Hall Room 110 - from 3pm to 4pm
We apologize for this inconvenience. If you have any questions, please feel free to contact ITS at x-7973 or its@manhattan.edu
Updates and news on how technology is changing in Manhattan University.
Friday, December 23, 2016
Classroom Technology Survey
Please take a few minutes to provide feedback on the latest generation Renovated Classroom. We will use this feedback when planning for future renovations.
Click here for the survey.
Click here for the survey.
Thursday, December 22, 2016
UPDATE - Scheduled Network Maintenance - Jan 3rd at 7am in RLC Building
UPDATE: The network maintenance was completed successfully this morning. Both wired and wireless networks in RLC should be up as of 9am this morning. If you have any network issues, please contact ITS at x-7973 or its@manhattan.edu. We apologize for the inconvenience.
ITS will be conducting network maintenance in RLC Building on Tuesday, January 3rd, which will cause some localized network outages between 7am and 9am.
In order to improve the network reliability, there will be scheduled network maintenance in order to replace some old and outdated network equipment. This network maintenance will affect both wired and wireless networks for the entire building.
We apologize for this inconvenience. If you have any questions, please feel free to contact ITS at x-7973 or its@manhattan.edu
ITS will be conducting network maintenance in RLC Building on Tuesday, January 3rd, which will cause some localized network outages between 7am and 9am.
In order to improve the network reliability, there will be scheduled network maintenance in order to replace some old and outdated network equipment. This network maintenance will affect both wired and wireless networks for the entire building.
We apologize for this inconvenience. If you have any questions, please feel free to contact ITS at x-7973 or its@manhattan.edu
Labels:
JasperNet,
JasperNet wireless
Wednesday, December 21, 2016
25Live Notifications Update
 One of the most requested features in 25Live has been the ability to receive a system-generated notification (email) when a requested event space had been approved. We are happy to report that this feature is now available and after weeks of testing has been activated for all users of 25live.
One of the most requested features in 25Live has been the ability to receive a system-generated notification (email) when a requested event space had been approved. We are happy to report that this feature is now available and after weeks of testing has been activated for all users of 25live. As of 12/21/2016, event/space requests submitted in 25Live will now include an email notification under the following conditions:
- Event Creation -
You will receive an email notification when you create an event confirming event details
- Event Change -
You will receive an email notification when a modification has been mode to your event by you or someone else.
- Location Approve/Deny -
You will receive an email notification when the space approver approves/denies your space request.
Tuesday, December 20, 2016
TOP TIPS FOR SAFE ONLINE HOLIDAY SHOPPING
Before you start your holiday shopping, remember to STOP. THINK. CONNECT.: Make sure security measures are in place, understand the consequences of your actions and behaviors and enjoy the benefits of the Internet.
- Keep a Clean Machine: All the devices you use for shopping - including smartphones and tablets - should have up-to-date software including security software, operating systems, programs and apps.
- When in Doubt, Throw it Out: Links in email, tweets, posts, and online advertising are often the way cybercriminals compromise your computer. If it looks suspicious, even if you know the source, it’s best to delete or if appropriate, mark as junk email.
- Think Before you Act: Be wary of communications that offer amazing deals that sound too good to be true, implore you to act immediately - including those about a problem with an order or payment or ask you to view the website via a provided link.
- Get Savvy about Wi-Fi Hotspots: Don’t share personal or financial information over an unsecured network (a connection that doesn’t require a password for access). Using the direct web access on your phone (via a 3G/4G connection) is safer than an unsecured wireless network when on your mobile device.
- Make Sure the Site is Legitimate: This includes a closed padlock on your web browser’s address bar or a URL address that begins with https. This indicates that the purchase is encrypted or secured. For new sites, check online reviews.
- Protect your Personal Information: Be alert to the kinds of information being collected to complete the transaction. Make sure the information requested is only that needed to complete the transaction. Only fill out required fields on checkout forms. Check the website's privacy policy. Make sure you understand how your information will be stored and used.
- Use Safe Payment Options: Credit cards are generally the safest option because they allow buyers to seek a credit from the issuer if the product isn’t delivered or isn’t what was ordered. Credit cards may have a limit on the monetary amount you will be responsible for paying. Never send cash through the mail or use a money-wiring service.
- Keep a Paper Trail: Save records of your online transactions, including the product description, price, online receipt, terms of the sale, and copies of email exchanges with the seller. Read your credit card statements as soon as you get them to make sure there aren’t any unauthorized charges. If there is a discrepancy, call your bank and report it immediately.
Monday, December 19, 2016
Monday, December 12, 2016
Google Drive Desktop App Ending Support for Windows XP, Vista and Server 2003
G Suite Update Alerts
Today, we’re announcing that on January 1, 2017 we will discontinue support for the Google Drive desktop app on Windows XP, Vista and Server 2003 since these platforms are no longer actively supported by Microsoft. The Google Drive desktop app (officially: "Google Drive for Mac/PC") will continue to function on these platforms, but will not be actively tested and maintained. If you are still on one of these unsupported platforms, we encourage you to move to a newer version of Windows to continue using Google Drive desktop app.
Today, we’re announcing that on January 1, 2017 we will discontinue support for the Google Drive desktop app on Windows XP, Vista and Server 2003 since these platforms are no longer actively supported by Microsoft. The Google Drive desktop app (officially: "Google Drive for Mac/PC") will continue to function on these platforms, but will not be actively tested and maintained. If you are still on one of these unsupported platforms, we encourage you to move to a newer version of Windows to continue using Google Drive desktop app.
Release track:
Launching to both Rapid release and Scheduled release on January 1, 2017
Reposted from the G Suite Update Alerts Blog
Originally Posted: 27 Oct 2016 11:26 AM PDT
Originally Posted: 27 Oct 2016 11:26 AM PDT
https://gsuiteupdates.googleblog.com/
Monday, December 5, 2016
Managing Your Online Reputation
More adults are using social media to stay connected both personally and professionally, which means recruiters (for college, sports, and jobs) may be using social media more frequently to assess candidates’ qualifications. The type of information shared on social media can also provide fodder for phishing attacks and even identity theft, or allow people to make assumptions about you based on the groups that you are affiliated with. Remember to check your social media privacy and security settings frequently to ensure careful online reputation management.
More adults are using social media to stay connected both personally and professionally, which means recruiters (for college, sports, and jobs) may be using social media more frequently to assess candidates’ qualifications. The type of information shared on social media can also provide fodder for phishing attacks and even identity theft, or allow people to make assumptions about you based on the groups that you are affiliated with. Remember to check your social media privacy and security settings frequently to ensure careful online reputation management.
Get the Word Out
Newsletter Content
You should understand how to present yourself on social networking sites and how to safeguard your information. What many may consider temporary or fleeting will most likely remain on the Internet forever. As a result, keep these dos and don’ts in mind when sharing online.
Dos
- Ask questions about who can access the information you are posting online, who controls and owns the information, and what is shared with third party.
- Maintain a backup of the content you post on professional networking sites (e.g., LinkedIn).
- Understand the default privacy settings on the social networking sites you use and how to change them to match your comfort level.
- Keep your personal information private. Assess whether it’s necessary to share sensitive information such as your birthday, mailing address, phone number, e-mail, mother’s maiden name, sexual orientation, or Social Security number.
- Be cautious about accepting requests to connect online. Connect only to people you trust who will not misuse the information you post.
- Check the location settings on photos and videos you post to social networking sites.
- Avoid joining online groups where you don’t know all the members or what they stand for.
- Use passphrases to protect your social media accounts. A passphrase is a set of words that create a phrase that is 20 to 30 characters long.
Don’ts
- Don’t share too much information that could be used to complete a profile about you. For example, share your birthday, but not the year you were born. Or share your hometown, but not the address where you live.
- Don’t share any information that is being used for verification purposes such as your mother’s maiden name, the name of your first pet, or the street where first lived. Consider making up alternate answers to those questions that only you would know.
- Don’t post when you are traveling or going out of town on vacation. It’s an open invitation letting criminals know that you are in a different location and that your home is vacant.
- Don’t post photos of inappropriate or illegal activities.
- Don’t click on attachments or links without checking the source.
- Don’t “check in” to every place you visit. That information could be used to identify you in a vulnerable location.
- Don’t use weak passwords, and never share your passwords!
Social Posts
- Our general rule: Never post anything #online you wouldn’t want your grandmother to see! #SocialMediaSafety
- Or to put it another way, if you wouldn’t want to see it on a billboard, keep it offline. #SocialMediaSafety
- The Internet is forever. Protect your online reputation—your older self will thank you! #SocialMediaSafety
- Keep your personal information private. Assess whether sensitive info is really necessary to share. #SocialMediaSafety
- Remember to check your social media privacy & security settings often! #SocialMediaSafety
Resources
- Learn how to protect yourself and your devices with these tips and resources from StaySafeOnline.org
- The Carnegie Cyber Academy offers suggestion for protecting your personal information
- US-CERT also provides tips for staying safe on social networking sites
- Read a book on the topic: lol...OMG! What Every Student Needs to Know About Online Reputation Management, Digital Citizenship, and Cyberbullying or Digital Drama: Staying Safe While Being Social Online.
- Read Jobvite’s findings in Welcome to the 2015 Recruiter Nation, Formerly Known as the Social Recruiting Survey
- Social Networking Fact Sheet (2014), Pew Research Center.
reposted from: http://er.educause.edu/blogs/2016/6/december-managing-your-online-reputation
Friday, December 2, 2016
Because your computer only has so much space
Aakash Sahney
PRODUCT MANAGER, GOOGLE DRIVE
Google Drive for Mac/PC — the app that syncs files on your computer with Google Drive — is an easy way to make sure your files are safe and accessible from anywhere. Today, some new features are rolling out that’ll make your syncing and sharing experience even better.
Drive can store terabytes (upon terabytes) but there’s a good chance your computer’s hard drive will run out of space if you sync everything. Fortunately, you can now select which folders or subfolders you want to sync — and deselect the ones you don’t.
When you deselect a folder, it’ll be removed from your computer but still kept safely in Drive. And Drive shows you the size of each folder, so you'll know how much space you're freeing up.
Take care of shared files and folders
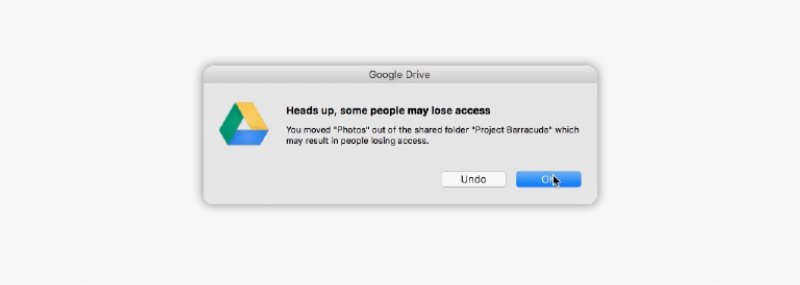
After you sync your files, Drive makes it easy to move and delete items directly from your computer. But doing that with shared files can cause others to lose access. Now, Drive warns you when this might happen.
Subscribe to:
Posts (Atom)