Below are precautions to protect you against the threat of ransomware:
- Update software and operating systems. Outdated applications and operating systems are the target of most attacks.
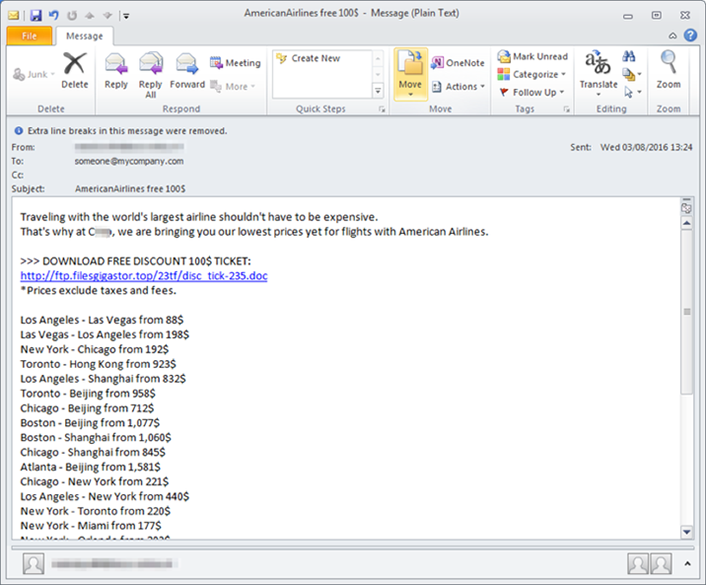
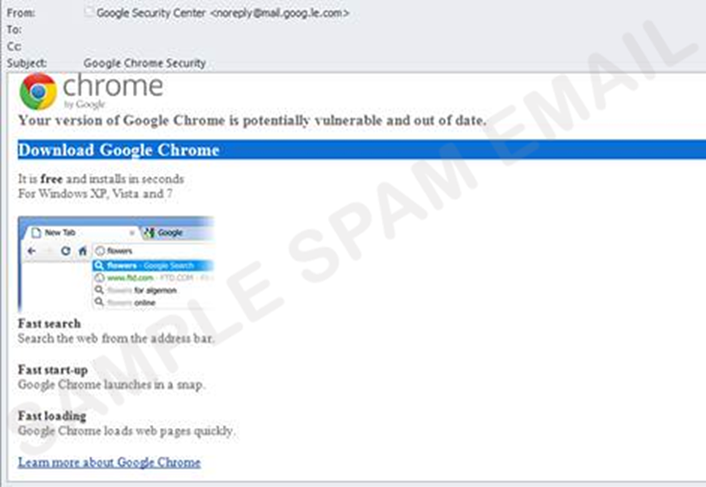
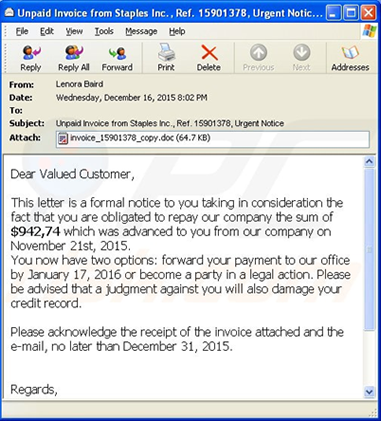
- Never click on links or open attachments in unsolicited emails.
- Backup data on a regular basis. Keep it on a separate device and store it offline.
- Restrict permissions to install and run software applications.
- Enable strong spam filters to prevent phishing emails from reaching you and authenticate inbound email to prevent email spoofing.
- Scan all incoming and outgoing emails to detect threats.
- Configure firewalls to block access to known malicious IP addresses.
For more information on Ransomware and how to defend against it please check out these articles: