We recently experienced a scam job opportunity email campaign. Do not assume that @gmail.com or @zohomail.com addresses offer job opportunities. The phishing email looked similar to the following.
Updates and news on how technology is changing in Manhattan University.
Friday, March 15, 2024
Act Fast! Weekly Stipend of $500!
We recently experienced a scam job opportunity email campaign. Do not assume that @gmail.com or @zohomail.com addresses offer job opportunities. The phishing email looked similar to the following.
Friday, January 12, 2024
New Year, Same Old Employment Phishing Campaigns
Wednesday, December 20, 2023
Foundational Cyber Security Awareness Course
A short foundational cyber security awareness course open to all members of the Manhattan College community
This course can be completed in under ten minutes and will guide you through how to identify and respond to the most common phishing attacks.
Do you focus your thoughts on creative solutions? Do you work well with others? Are you results-oriented?
Malicious criminals who use phishing tactics hope you are and to use your behavior against you. Please use care for your welfare and talk to your loved ones for their benefit of their welfare.
Friday, December 1, 2023
Hiring Offer That Requires Use of a non-@manhattan.edu Email Address
 |
| "I assure you" meme regarding how we're not hiring remote student research positions that requires one hour of work for $370/week. |
If you were not scammed, maybe a friend is in the process of being scammed. Talk to your friends about this. Maybe someone you care about will be impacted by this if you do not.
Wednesday, November 8, 2023
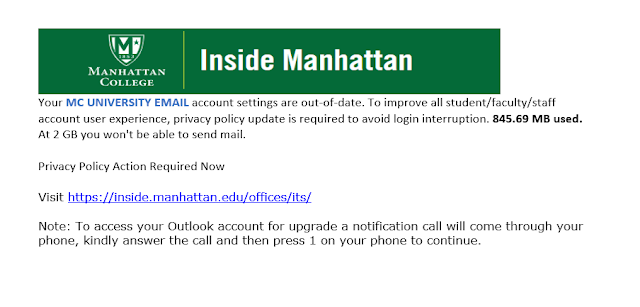
Stay alert -- Employee Benefit Scam
This morning many phishing campaign emails announcing an "employee benefit" were delivered successful to our Gmail-secured inboxes.
The emails are similar to the following
From: Leszek Buller <l.buller@uksw.edu.pl>
Subject: 2023 Employees Benefit Program
Dear Employee,
We hope this message finds you in good health and high spirits. We
understand that the past year has been challenging for many, and we want to
extend our support during these difficult times. We are excited to
introduce the 2023 Employees Benefit Program, designed to provide financial
assistance to our valued families and employees.
As part of our ongoing commitment to your well-being, we have established a
program that aims to ease financial burdens and provide some relief. We
have allocated funds to provide *$700* to each family and employee that
meets the designated criteria.
If you or your family have experienced financial hardship and could benefit
from this program, we encourage you to apply. The application process is
now open and will remain so until *November 20, 2023*. To apply, sign in
using the link provided below:
Employees Benefit Program
Sincerely,
*2023-EBP support team*
The hyperlink's URL is an agilecrm.com hosted credential harvesting form. If you happened to share your credentials or if you are unsure if you did, please change your JasperNet password.
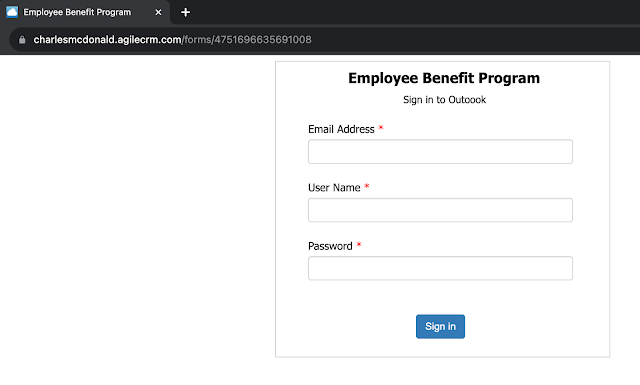 |
| Credential harvesting form. |
Friday, May 19, 2023
Ongoing "Student Employment" scam
The emails are similar to the following
Wednesday, May 3, 2023
How ITS Deals With Phishing Email Campaigns
Friday, March 3, 2023
"Vector LMS, Higher Education Edition Online Learning" is not a phishing attack
Between March 2nd 11:45PM and March 3rd 12:30AM, safecolleges.com sent ~1100 emails to our community. These emails are legitimately from a vendor that Human Resources does business with.
 |
| Gmail displays a warning banner with a convenient "report phishing" button for most of the safecolleges.com emails. |
Do not report these emails as phishing attempts. This email campaign helps the college comply with New York State law regarding sexual harassment.
Wednesday, March 1, 2023
Payroll Phishing Campaign
A malicious actor is sending paycheck picture attachments via email from a forged email address, payrolldepartment@manhattan.edu. An example email is included below.
These emails are "unauthenticated" by which that means the sending SMTP (email) server is not allowed to send as any @manhattan.edu address. ITS prevents delivery of such emails to ITS managed @manhattan.edu accounts. ITS also uses DMARC to notify all receiving SMTP (email) servers to be as careful as possible with unauthenticated @manhattan.edu emails. Unfortunately, DMARC is just a suggestion and not a command. So unauthenticated @manhattan.edu emails may still be delivered to phishing targets.
From: Payroll Department
Date: Wed, Mar 1, 2023 at 1:39 PM
Subject: **PAYCHECK**
To: [redacted]
Good Day [redacted],
You are receiving this e-mail because your information has been registered and will be
scheduled for weekly payments directly from the Payroll department. The Paycheck that
covers the expenses for the office supplies you will be working with is attached in this
email. A Sales Representative will be assigned to assist you with the purchase of these
items once the funds are available from this deposit. Immediately proceed to make a mobile
deposit and contact your professor in charge once completed for clearance purposes.
Further Assignments as well as your employment documents will be sent once the supplies
are delivered. Kindly inform your professor letting him know that you have received this
email.
I have outlined Instructions on how to make a mobile deposit below.
Print out and cut it to a ( check size/shape ) At the back of your check endorse by
writing your
Full name
Mobile Deposit Only
Your account number
Sign.
Once you are done, you make a mobile deposit on your mobile banking app
Thank You.
Best Wishes,
Payroll Department.
Please do not reply to this email message. It was sent from a notification-only address
that cannot accept incoming emails.
--
Respectfully,
Office of Financial Aid Administration
4513 Manhattan College Parkway
Riverdale, NY 10471
Phone: 718-862-7100
Fax: 718-862-8027
Monday thru Friday
9:00 am to 4:30 pm
manhattan.edu/finaid
Tuesday, February 28, 2023
Job Opportunity Scam
This afternoon a malicious actor, using a compromised @manhattan.edu account, sent over 2,500 phishing attempts to our organization.
If you received such a message please do not reply to it and do not follow its instructions. If you have already interacted with the malicious actor, do not do so anymore.
Monday, December 19, 2022
Peering into the Email Quarantine
ITS makes use of Gmail's compliance rules (that are defined by our Google Workspace administrators) to automatically quarantine incoming or outgoing emails.
A recent phishing trend is not to use any visible text in the message body and instead use an image contained within a hyperlink that directs to a malicious login page.
Thankfully all of these phishing emails were never delivered to inboxes, spam folders, etc. They matched an existing email compliance rule and were delivered in our organization's email quarantine.
Saturday, April 2, 2022
Phishing Reminder
Everyday is a chance to do good. Or in the case of phishers, to do evil.
Today, ITS detected a phishing email campaign aimed at the Manhattan College community. The phishing email claims to be from the college's "Manhattan Mail Delivery Subsystem." It requests the user to click a phishing link (that displays a manhattan.edu URL but actually directs to an absolutely different domain), login with their credentials and review undelivered email messages.
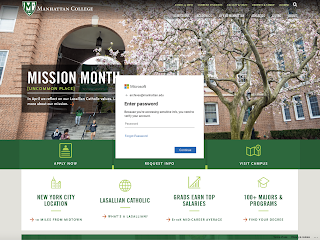 |
| Phishing login webpage that is aimed at the Manhattan College community. |
Everyday the college receives phishing campaigns. This particular campaign is notable due to the branding of the phishing login webpage. Notice the differences between this phishing login webpage and the official login webpage that you typically use. Now consider that the phishers could copy the official login webpage's design.
Wednesday, October 6, 2021
Phishing Campaign -- $1,499 iCloud Orders
Today multiple gmail.com accounts sent emails to a fraction of our organization. The emails claim that the recipient would be charged $1,499 for their 12TB iCloud storage plan.
This is a good opportunity to announce that October is Cyber Security Awareness month. Best to keep in mind that any email may be a scam and we all are one degree away from criminals.
The most common IT crime still is Business Email Compromise (BEC) even though ransomware is increasing rapidly. It is best to be mindful of how to parse an email address and to do your best to understand who is emailing you.
Email addresses are formed by concatenating a username with the '@' sign and with a domain (e.g., bob@example.com). Sometimes people are confused by the common phishing addresses that use a domain inside the username (e.g., bob.manhattan.edu@example.com). Understand that such email addresses are available to anyone including to criminals.
If you receive a phishing email, you can report it to Gmail if you're using the web interface (not the Gmail mobile app, unfortunately). Google will alert ITS!
 |
| Gmail's 'Report phishing' feature is under a vertical ellipsis in the upper-right of an email. |
You can also forward the email to its@manhattan.edu. If you are unsure if an email is a phishing email, please forward it to its@manhattan.edu. We can help to determine what is what and if necessary report the email as a phishing attempt to Google.
Wednesday, April 28, 2021
Phishing Security Refresher
Phishing is the practice of sending fraudulent emails that resemble emails from reputable sources. The aim is to steal sensitive data like credit card numbers and login information. It’s the most common type of cyber attack.
Phishing attacks are designed to trick users into taking actions that are not in their best interests. They can be avoided by doing the following:
- Verify message sender
- Before clicking a link, verify that it goes to where it claims by hovering over it and checking the destination URL and browse to the target site directly in your browser.
- Be cautious of attachments. Do not open a file that you’re not expecting.
- Don’t enter your credentials into a site that you do not recognize.
- Create a SPAM filter that detects viruses and blank senders.
Friendly Reminders:
- You should always inform ITS of any suspicious emails you receive but when in doubt, forward the email in question to its@manhattan.edu so we can verify
- If you would like help setting up filters in your email you can use this link to put in a service request and a member of our Training Team will schedule a 1:1 appointment with you.
Friday, August 14, 2020
Messages from mcs.manhattan.edu Sent Unintentionally
If you receive a message from Admin User mcs.manhattan.edu these are legitimate emails that were unintentionally sent to the community. A sample is shown below:
The email is safe.
Friday, February 28, 2020
Phishing with Viruses

2020 seems to have come in strong by hurdling the Coronavirus (COVID-1) at us pretty quickly! Now that we have more information, we can take preventative steps to keep from getting sick. However, cyber criminals are now using the Coronavirus to try and steal your sensitive information and it's just as important to take preventative measures to keep your cyber presence safe as well.
- Make sure to verify the sender by checking their email address. If it is coming from the World
Health Organization (WHO) the email address should read “person@who.int”.
No other email addresses are used by the WHO.
- Make sure the link is correct before clicking on it. The link should only begin with
‘https://www.who.int.’If you are still unsure, do
not click the link you received- open up your browser and navigate the WHO
website to check if it is valid.
- Be cautious when providing sensitive info. Use extra caution when giving
your username and password, and credit card info out. Most of the
information on the WHO website is public info and will not require a
username and password.
- Don't feel pressured to make any quick decisions. Cyber criminals rely on your
panic instincts and will use this to try and get you to give them your
personal information. Take a moment to think of whether or not it is
appropriate that you are receiving this request.
- If you did give sensitive information out, don't panic. Change the credentials that you
gave out, as soon as you can.
- If you suspect something is a scam report. Trust your gut. If you think
something is wrong, report it! This will help to spread awareness about
the scam and help organizations to block potential scammers. To report
a scam to the WHO please follow the instructions here.
Thursday, December 19, 2019
PROTECT Your Account - Holiday Break Safeguards
ITS will NOT ASK for you to update your password or other personal information.
ITS will NOT DISABLE your account over the break if you do not respond to an email.
As we approach the Christmas Holiday break, ITS would like to remind campus users that we will NOT be performing updates and will NOT ASK for information from you. Phishing attacks are on the rise and we are taking steps to prevent these attacks from affecting Manhattan College.
If you receive an email or other communication requesting personal information or asking you to update your password - DO NOT RESPOND. These messages should be reported to ITS or the sending office for validation.
Below are some additional resources that were previously provided to the campus community:
Holiday Scams and Malware Campaigns
Phishing Infographics
Half of all Phishing Sites Now Have the Padlock
Sunday, December 8, 2019
Avoid Online Scams this Holiday Season!
Let's identify the different types of scams that you should keep an eye out for:
Fake online shops
As the retail rush ramps up, fake online stores pop up to prey on our desire for a bargain. Sometimes, these sites will be poorly designed, but the scammers are betting that, in the festive rush, enough people will be too distracted to be able to tell the difference between these sites and legitimate “pop-up” shops. When shopping on sites such as Amazon, be sure to check who the seller is. Not all items on Amazon are sold by Amazon. Some sellers may be third party or individual sellers, so be sure to check their reputation if the item is not sold by Amazon.Tip: Look for online reviews and think about phoning the contact number. If there isn’t one, this could be a warning sign.
Charity phishing
Scammers know that many people feel charitable at this time of year and so they target your good will. They may send emails from a bogus charity or ones that purport to come from a legitimate charity but contain a link to a scam site.Tip: If you want to give to good causes during the holidays, go through the charity in question’s own site.
Fake delivery emails
In the run-up to the holidays, many people have dozens of packages arriving and often lose track of what they’ve ordered. Scammers know this and send out emails that purport to come from legitimate courier companies. These ask recipients to click on a link. When they do, they download malware or are taken to a scam site.Tip: Check the sender’s address to ensure it is a legitimate company and go to the company’s own website to track orders.
Wish list scams
Wish lists are a way for people to post what gifts they want online. However, these are often easy for anyone to view and, for a fraudster, can be a goldmine. Such lists often contain personal information and this makes the list owner vulnerable to identity theft. Cyber-criminals can also use items on the list for targeted phishing scams.Tip: Ensure the privacy settings on any online lists are set to high.
E-voucher scams
These are often shared on social media or email and claim to offer free vouchers from well-known brands. Potential victims are told that, to claim a voucher, all they need to do is click on a link. This can take them to a fake site where they will be asked for their details.Tip: Look out for poor grammar and, if in any doubt, check the voucher by emailing the shop.
Social media scams
Scammers use social media to tempt people with irresistibly good deals on goods such as electronics and jewelry. The social networks are also a place where links to phishing sites and malware can be widely shared. Scammers may even be “friends” of real friends of yours who say yes to every connection request.Tip: The best defense here is not to click on links that look even remotely suspicious.
[1] Christmas Spending Statistics
Partially reposted from Six Scams to Look Out for this Christmas
Sunday, November 10, 2019
How Can Higher Ed Better Prepare Cybersecurity Students for a Hot Job Market?
- Hold informational sessions on cybersecurity. Help spread the word on your campus about the cybersecurity skills gap and job opportunities. You could ask your CISO or information security team to conduct a cybersecurity seminar or invite local experts to share their knowledge and expertise with your students. The Enterprise Security Team at The Ohio State University has already implemented this idea, and they sponsor an annual and free on-campus Cybersecurity Days to expand knowledge of security and data protection for their entire college community.
- Sponsor or encourage membership in student associations. There are two student cybersecurity organizations for your students to explore—NationalCybersecurity Student Association and Women in CyberSecurity (WiCyS. The National Cybersecurity Student Association has a number of resources on their website, and you can sign up for their newsletter or follow their Snapchat account to view a day in the life of a cyber student or industry professional. The WiCyS is dedicated to bringing together women in cybersecurity from academia, research, and industry to share knowledge, experience, networking, and mentoring. You can also explore setting up a local WiCyS student chapter on your campus.
- Offer campus internships. In addition to knowledge of advanced cybersecurity concepts, the most important qualification for cybersecurity employment is relevant work experience. You can help your students by hiring them as interns in your institution's information security department. This offers students real-world experience while providing supplemental staffing for your department. For suggested qualifications and responsibilities, use the Information Security Intern Job Description Template on the EDUCAUSE website as a starting point.
- Identify scholarship opportunities. The CyberCorps: Scholarship for Services, funded by the NSF, provides up to $22,500 per year for undergraduates and $34,000 per year for graduate students. In return, students commit to work in a for a federal, state, or local agency for a period matching the length of their scholarship. The Cyber Security Degree website provides a comprehensive list of additional cybersecurity scholarships and other career resources.
- Encourage students to deepen their knowledge. The NICCS Education Training Catalog is a central location where cybersecurity professionals across the nation can find more than 3,000 cybersecurity-related courses. Anyone can use the interactive map and filters to search for courses offered in their local area to add to their skill set, increase their level of expertise, or earn a certification. You could also direct your students to take advantage of the free online courses offered through edX, US Department of Homeland Security, Cybrar, or SANS Cyber Aces Online.
- Attend cyber competitions. Institutions with an information assurance or computer security curriculum can give their students an additional way to hone their skills and have fun by participating in regional events hosted by the National Collegiate Cyber Defense Competition(NCCDC). The top regional teams can then go on to the National Championship, which was won by University of Virginia in 2018. Another cybersecurity competition for high school and college students is the National Cyber League (NCL), is a defensive and offensive puzzle-based, capture-the-flag style competition. All participants play the games simultaneously and are tested with real cybersecurity challenges they will likely face in the workforce.
- Participate in cybersecurity conferences. Students may be interested the educational and networking opportunities from attending the annual conferences for the National Cybersecurity Student Association or Women in CyberSecurity. For additional conferences in your area, InfoSec publishes a comprehensive list with hundreds of cybersecurity events in the United States, Europe, and Asia.
Sunday, October 27, 2019
Top Tips to Securely Using Social Media
Overview
Posting
Privacy
Passphrase
Lock Down Your Account
Scams
Terms of Services
Work
Reach out to IT Services with any questions:
- Email: its@manhattan.edu
- Call: 718-862-7973