As you may be aware, there was an email outage late Friday April 22nd into Saturday April 23rd morning. Messages sent to Manhattan College emails during this time are lost. If you sent any important messages during this time frame, please resend. The outage was repaired by 10AM Saturday April 23rd.
Updates and news on how technology is changing in Manhattan University.
Monday, April 25, 2022
Tuesday, February 23, 2021
mancol.edu Email Alias Termination
On March 1st, 2021, Manhattan College will terminate @mancol.edu email aliases. The domain manhattan.edu has been Manhattan College’s primary domain since 1996 and the domain mancol.edu has been legacy since that time.
The majority of our community does not use @mancol.edu. During December all users sending email with their @mancol.edu email alias or receiving email with their @mancol.edu email alias were notified of this termination.
Update any mailing list subscriptions, professional online accounts, etc. to use your @manhattan.edu email address and use your @manhattan.edu email address to send email.
If you have any questions or concerns please contact ITS at its@manhattan.edu.
Thursday, October 22, 2020
Google Workspace New Dynamic Emails Feature
Google Workspace Update
This update makes it easier to manage access requests to Google Drive files by sending dynamic emails. Dynamic emails allow you to respond to the request without leaving Gmail.
When someone requests access to a Google Drive file, you’ll receive an email with the access request. The email lets you review the request, choose the access level and grant access directly from the email. It will work for Gmail on the web, on Android devices and on Apple devices.
Thursday, June 11, 2020
Manage Multiple Google Accounts with Ease using Delegated Accounts or Chrome Profiles
Delegate accounts: you may want to give access to your email account to another person. Mail delegation allows the delegate to read, send, and delete messages on your behalf through their own account. Please reference this article for how to set up a Delegated Account.
For example, a manager can delegate email access to another person in their organization, such as an administrative assistant. Another great use for delegation is shared email accounts
1. Delegated accounts cannot be accessed via mobile applications, ONLY on computers.
2. After a delegated email is set up, it may take a few seconds to a few hours for the changed to reflect in your account. Please refresh the tab where the account is open frequently until you see the change has been applied.
Friday, March 22, 2019
Phishing quiz
Google and Jigsaw have developed a phishing quiz, which everyone should take. Only eight emails are posed and you have to determine if they are legitimate or not. Go, go, go!
Monday, March 18, 2019
Week 4 Tech Showcase -Mail Merges Made Easy Using formMule
formMule
- use auto-insert merge tags with the click of a button, making template-creation a breeze!
- use up to 10 different email templates based on specified send conditions.
- create unique case numbers on form submit for use in keying follow-ups
- grab and send form response edit URLs, and formulas copied down on form submit
- use custom spreadsheet functions RANGETOTABLE and RANGETOVERTICALTABLE which make it possible to merge tables of multiple, matching records into email bodies.
Another powerful application of formMule is to mail merge Google Form responses.
Please watch this video for additional help getting started with formMule:
Please take this brief formMule for Mail Merges Survey to let us know what you think about formMule.
If you have additional questions about how to use formMule for mail merges please contact IT Services:
ITS@manhattan.edu or TEL: 718-862-7973
Friday, October 26, 2018
Extortion Emails Did Not Stop
Did you forget our July 2018 extortion email blog post? We didn't. Extortion emails including an old breached password from a non Manhattan College affiliated computer service (e.g., LinkedIn, Tumblr, Adobe, etc.) have been continuing to arrive to Manhattan College community email inboxes demanding money or else the extortionists will release risqué videos.
From September 17th until October 16th, we received 32,474 emails with a subject that began with Your password is. They were aimed at 576 different manhattan.edu accounts and used 977 throwaway email accounts to send the messages.
- Several password best practices to consider: Use a password manager to store a distinct, random password per company you do business with.
- Never use your JasperNet password elsewhere.
- If you know that one of your accounts has been breached, whatever password was used is now compromised and can never be used again.
- Do not use passwords such as Homework2 or password123 and instead use passwords that are longer & are not mostly dictionary words.
- Always reach out to ITS when a dialogue is desired.Email: its@manhattan.edu or TEL: 718-862-7973
Also consider signing up for password breach alerts. You can use a website such as Have I Been Pwned or a browser-based solution such as Firefox Monitor.
A few popular password managers are on the market. Remember that you can use distinct, random passwords using the following sites: LastPass (free), DashLane (free), or 1Password (30 day free trial). You must make sure that your master password to your password manager is never lost and that you must do regular backups of your password vaults. If you lose your master password, you will not be able to access your password vault.
How to Protect Yourself From Scams Like This:
Step up to Stronger Passwords
I Clicked on a Phishing Scam Email... What now?
Partially reposted from: 10/25/18 Harvested Passwords Used in Email Extortion | AT&T ThreatTraq
Tuesday, July 24, 2018
Extortion emails incoming!
The extortion message follows a template.
I do know blahblahpassword is your password. Lets get directly to the point. You do not know me and you're most likely thinking why you're getting this mail? None has paid me to check about you.By including a valid password, the extortionist aims to establish legitimacy. A few of the details are technically possible such as an RDP attack or recording from the webcam.
Well, I setup a software on the porn site and do you know what, you visited this site to have fun (you know what I mean). When you were viewing videos, your web browser began functioning as a Remote Desktop that has a keylogger which provided me accessibility to your screen and web cam. Just after that, my software obtained all your contacts from your Messenger, social networks, and email.
You have just two choices. Let us read these types of options in particulars:
Very first solution is to skip this message. In this case, I most certainly will send your very own video clip to almost all of your contacts and thus just think concerning the disgrace you will get. Moreover if you happen to be in a relationship, exactly how it is going to affect?
Second alternative will be to give me $7000. I will think of it as a donation. As a consequence, I most certainly will quickly discard your video footage. You could resume your daily life like this never occurred and you surely will never hear back again from me.
You will make the payment through Bitcoin (if you don't know this, search "how to buy bitcoin" in Google search engine).
Should you are planning on going to the cop, anyway, this email message can not be traced back to me. I have covered my actions. I am just not looking to charge a fee so much, I just want to be compensated. You have one day in order to make the payment. I've a unique pixel within this mail, and now I know that you have read this email message. If I do not receive the BitCoins, I will certainly send your video to all of your contacts including close relatives, colleagues, and so on. Nonetheless, if I receive the payment, I'll destroy the recording right away. If you need evidence, reply Yea and I will certainly send your video to your 7 contacts. It is a non-negotiable offer, therefore please do not waste my personal time & yours by responding to this email.
If the extortionist had done any of this then, they would name the specific porn site or provide images from the webcam.
If you receive this message, please do the following:
- immediately change your password for any site where you used the hacked password;
- send its@manhattan.edu the extortion message including the full headers using these directions;
- and, sign up for data breach notifications at haveibeenpwned.com by clicking the "Notify me" link at the top of the page.
Thankfully, this is appears to be an automated message using email addresses and hacked passwords. But if the extortionists were assiduous then, they would include pictures from social media accounts or from friends' social media accounts.
Sextortion is a horrible crime. The FBI's sextortion news page shows a sample of how awful it can be. If a loved one is a victim of sextortion please report it to the FBI 1-800-CALL-FBI (1-800-225-5324).
Friday, September 22, 2017
Inbox by Gmail
Overview to Inbox by Gmail
Inbox offers a more productive way to review your email. Inbox still syncs to Gmail and has an effect on how email is handled there. Terms like "marked as read", and "archived" are deliberately phased out. Instead, Inbox treats your emails like to-dos. The app assumes that you need to do something with every email. Some are critical pieces of information you need to sort or set aside, some demand replies, and some inform you that you need to do something outside your inbox like pay a bill.
In all of those cases, "reading" an email doesn't mean you're done with it, so why treat it as such?
The Three Classes of Email: Pinned, Snoozed, or Done

- Pin: When you pin an email, it gets more prominent placement in your inbox. If it's something you'll need to come back to like travel confirmation, reference documents, or an important conversation, pinning it is probably the right way to go.
- Snooze: You may need an email but not necessarily right now. Inbox allows you to snooze it so it disappears from your inbox and comes back at a later time. You can specify a specific time, use vague presets like "tomorrow afternoon" or let Google decide with a "Someday" option for things you don't want to deal with now, but that aren't time-sensitive. If you view your inbox in Gmail, snoozed messages will be archived.
- Done: This is for when you don't need a message anymore. Marking an email as "Done" removes it from your inbox or visible bundles. You can still search for it, but it won't be cluttering everything up. In Gmail this also archives your messages and the functionality is similar in Inbox.
 |
| SWIPE FEATURE |
Click here to get Inbox by Gmail and review highlights and videos of the features.
Partially reposted from https://www.google.com/inbox/
Tuesday, January 17, 2017
New InBox by Gmail
Overview to Inbox by Gmail
Inbox offers a more productive way to review your email. Inbox still syncs to Gmail and has an effect on how email is handled there. However, the question is the bigger problem. Terms like "marked as read", and "archived" are deliberately phased out. Instead, Inbox treats your emails like to-dos. The app assumes that you need to do something with every email. Some are critical pieces of information you need to sort or set aside, some demand replies, and some inform you that you need to do something outside your inbox like pay a bill.
In all of those cases, "reading" an email doesn't mean you're done with it, so why treat it as such?
The Three Classes of Email: Pinned, Snoozed, or Done

- Pin: When you pin an email, it gets more prominent placement in your inbox. If it's something you'll need to come back to like travel confirmation, reference documents, or an important conversation, pinning it is probably the right way to go.
- Snooze: You may need an email but not necessarily right now. Inbox allows you to snooze it so it disappears from your inbox and comes back at a later time. You can specify a specific time, use vague presets like "tomorrow afternoon" or let Google decide with a "Someday" option for things you don't want to deal with now, but that aren't time-sensitive. If you view your inbox in Gmail, snoozed messages will be archived.
- Done: This is for when you don't need a message anymore. Marking an email as "Done" removes it from your inbox or visible bundles. You can still search for it, but it won't be cluttering everything up. In Gmail this also archives your messages and the functionality is similar in Inbox.
 |
| SWIPE FEATURE |
Click here to get Inbox by Gmail and review highlights and videos of the features.
Partially reposted from https://www.google.com/inbox/
Wednesday, December 21, 2016
25Live Notifications Update
 One of the most requested features in 25Live has been the ability to receive a system-generated notification (email) when a requested event space had been approved. We are happy to report that this feature is now available and after weeks of testing has been activated for all users of 25live.
One of the most requested features in 25Live has been the ability to receive a system-generated notification (email) when a requested event space had been approved. We are happy to report that this feature is now available and after weeks of testing has been activated for all users of 25live. As of 12/21/2016, event/space requests submitted in 25Live will now include an email notification under the following conditions:
- Event Creation -
You will receive an email notification when you create an event confirming event details
- Event Change -
You will receive an email notification when a modification has been mode to your event by you or someone else.
- Location Approve/Deny -
You will receive an email notification when the space approver approves/denies your space request.
Monday, November 7, 2016
Gmail and Google Calendar get a whole lot better on iOS
The new Gmail app for iOS
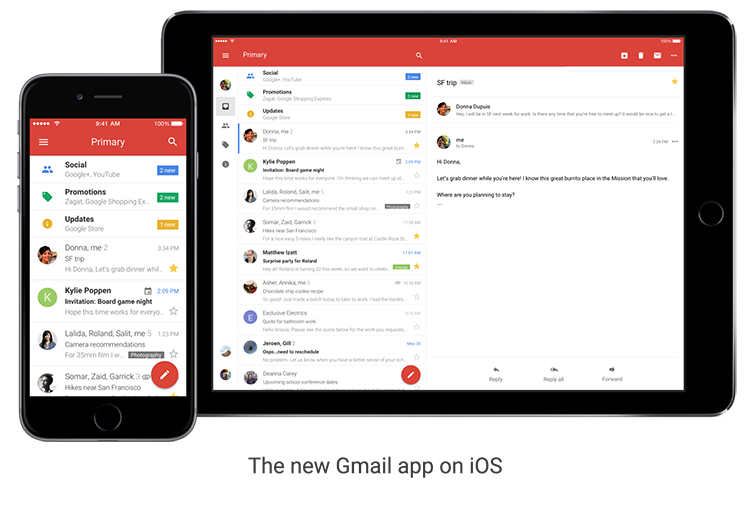
- Undo Send, just like you do on the desktop, to prevent embarrassing email mistakes
- Search faster with instant results and spelling suggestions (like when you type “flighht,” but you really meant “flight”)
- Swipe to archive or delete, to quickly clear items out of your inbox
Google Calendar: Updated for you
- Month view and week in landscape view, so you have even more ways to see your schedule at a glance.
- Spotlight Search support, so you can search for events, Reminders and Goals in Apple’s Spotlight Search and find what you’re looking for faster.
- Alternate calendars. If you often look up dates in a non-Gregorian calendar — like Lunar, Islamic, or Hindu — you can now add that calendar to easily see those dates alongside your current calendar.

Tuesday, September 13, 2016
Tuesday, January 19, 2016
Keep Control of Your Jaspernet Account... Make Sure that Your Personal Email is On File!
Please follow the instructions here to update your personal email address on file.
Thursday, October 1, 2015
Issue RESOLVED: Email Notifications
 An issue that we recently identified regarding email notifications from campus services has been resolved. We have confirmed that email notifications are now being reliably sent and received from the Moodle and 25Live systems. You can find the original notification here: http://itsblog.manhattan.edu/2015/09/identified-issue-email-notifications.html
An issue that we recently identified regarding email notifications from campus services has been resolved. We have confirmed that email notifications are now being reliably sent and received from the Moodle and 25Live systems. You can find the original notification here: http://itsblog.manhattan.edu/2015/09/identified-issue-email-notifications.htmlIf you continue to experience issues receiving email, please contact ITS Client Services at x7973 or its@manhattan.edu #TellITS
Monday, September 28, 2015
Identified Issue: Email Notifications from Some Campus Services Not Being Received
 ITS has identified an issue where email messages from campus systems such as Moodle, 25Live, and others are not being forwarded to their intended recipients. ITS has opened a support ticket with Google (Gmail) and has taken steps to update email configurations to mitigate the issue. To date, these steps have not resolved the issue and we continue to work with Google and others to implement a solution that allows all campus systems to reliably send email messages.
ITS has identified an issue where email messages from campus systems such as Moodle, 25Live, and others are not being forwarded to their intended recipients. ITS has opened a support ticket with Google (Gmail) and has taken steps to update email configurations to mitigate the issue. To date, these steps have not resolved the issue and we continue to work with Google and others to implement a solution that allows all campus systems to reliably send email messages.If you are experiencing similar issues with JasperNet services not listed above, please inform ITS by emailing its@manhattan.edu
UPDATE:
Despite email notifications not being received, all systems are functioning normally. Until this issue is resolved, it is recommended that users connect to the affected systems to retrieve information.
Monday, April 20, 2015
Email Phishing Attacks - When to be suspicious and what to do before clicking that link.....
A series of messages received over the weekend has generated a lot of questions to the ITS Client Services Helpdesk asking "Is this Legit?". As with most messages, the message contained a warning about email quota or account security and was supposedly from "The Helpdesk". The messages also directed users to click on a malicious link in an attempt to capture their account information.
If you receive a suspicious message, please contact ITS to verify authenticity before providing your account credentials or any personal information.
A copy of one of these messages is below:
Clicking the link brings users to an unbranded page with some generic wording and solicits the username, email address, and password of the user:
Take a moment to run through Google's Security Checkup. The Security Checkup will insure that recent activity on your account is legitimate, that the add-ins accessing to your account are legitimate, and that the forwarding addresses that have been configured in gmail are legitimate:
Tuesday, February 10, 2015
Today is "Safer Internet Day"
Thursday, November 6, 2014
Phishing attacks on the Rise
A recent poll in the U.S. showed that more people are concerned about being hacked than having their house robbed. That’s why we continue to work hard to keep Google accounts secure. Our defenses keep most bad actors out, and we’ve reduced hijackings by more than 99% over the last few years.
We monitor many potential threats, from mass hijackings (typically used to send lots of spam) to state-sponsored attacks (highly targeted, often with political motivations).
This week, we’re releasing a study of another kind of threat we’ve dubbed “manual hijacking,” in which professional attackers spend considerable time exploiting a single victim’s account, often causing financial losses. Even though they’re rare—9 incidents per million users per day—they’re often severe, and studying this type of hijacker has helped us improve our defenses against all types of hijacking.
Manual hijackers often get into accounts through phishing: sending deceptive messages meant to trick you into handing over your username, password, and other personal info. For this study, we analyzed several sources of phishing messages and websites, observing both how hijackers operate and what sensitive information they seek out once they gain control of an account. Here are some of our findings:
- Simple but dangerous: Most of us think we’re too smart to fall for phishing, but our research found some fake websites worked a whopping 45% of the time. On average, people visiting the fake pages submitted their info 14% of the time, and even the most obviously fake sites still managed to deceive 3% of people. Considering that an attacker can send out millions of messages, these success rates are nothing to sneeze at.
- Quick and thorough: Around 20% of hijacked accounts are accessed within 30 minutes of a hacker obtaining the login info. Once they’ve broken into an account they want to exploit, hijackers spend more than 20 minutes inside, often changing the password to lock out the true owner, searching for other account details (like your bank, or social media accounts), and scamming new victims.
- Personalized and targeted: Hijackers then send phishing emails from the victim’s account to everyone in his or her address book. Since your friends and family think the email comes from you, these emails can be very effective. People in the contact list of hijacked accounts are 36 times more likely to be hijacked themselves.
- Learning fast: Hijackers quickly change their tactics to adapt to new security measures. For example, after we started asking people to answer questions (like “which city do you login from most often?”) when logging in from a suspicious location or device, hijackers almost immediately started phishing for the answers.
- Stay vigilant: Gmail blocks the vast majority of spam and phishing emails, but be wary of messages asking for login information or other personal data. Never reply to these messages; instead, report them to us. When in doubt, visit websites directly (not through a link in an email) to review or update account information.
- Get your account back fast: If your account is ever at risk, it’s important that we have a way to get in touch with you and confirm your ownership. That’s why we strongly recommend you provide a backup phone number or a secondary email address (but make sure that email account uses a strong password and is kept up to date so it’s not released due to inactivity).
- 2-step verification: Our free 2-step verification service provides an extra layer of security against all types of account hijacking. In addition to your password, you’ll use your phone to prove you’re really you. We also recently added an option to log in with a physical USB device.
Take a few minutes and visit the Secure Your Account page, where you can make sure we’ve got backup contact info for you and confirm that your other security settings are up to date.




