To the Manhattan University Community,
Chief Information Officer
Information Technology Services

Updates and news on how technology is changing in Manhattan University.
To the Manhattan University Community,

 |
| "I assure you" meme regarding how we're not hiring remote student research positions that requires one hour of work for $370/week. |
This morning many phishing campaign emails announcing an "employee benefit" were delivered successful to our Gmail-secured inboxes.
The emails are similar to the following
From: Leszek Buller <l.buller@uksw.edu.pl>
Subject: 2023 Employees Benefit Program
Dear Employee,
We hope this message finds you in good health and high spirits. We
understand that the past year has been challenging for many, and we want to
extend our support during these difficult times. We are excited to
introduce the 2023 Employees Benefit Program, designed to provide financial
assistance to our valued families and employees.
As part of our ongoing commitment to your well-being, we have established a
program that aims to ease financial burdens and provide some relief. We
have allocated funds to provide *$700* to each family and employee that
meets the designated criteria.
If you or your family have experienced financial hardship and could benefit
from this program, we encourage you to apply. The application process is
now open and will remain so until *November 20, 2023*. To apply, sign in
using the link provided below:
Employees Benefit Program
Sincerely,
*2023-EBP support team*
The hyperlink's URL is an agilecrm.com hosted credential harvesting form. If you happened to share your credentials or if you are unsure if you did, please change your JasperNet password.
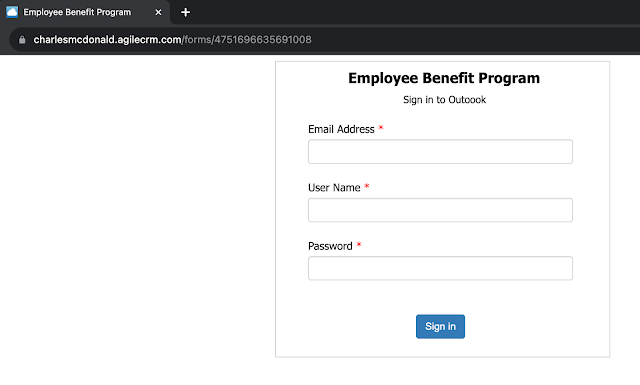 |
| Credential harvesting form. |
The emails are similar to the following
Between March 2nd 11:45PM and March 3rd 12:30AM, safecolleges.com sent ~1100 emails to our community. These emails are legitimately from a vendor that Human Resources does business with.
 |
| Gmail displays a warning banner with a convenient "report phishing" button for most of the safecolleges.com emails. |
Do not report these emails as phishing attempts. This email campaign helps the college comply with New York State law regarding sexual harassment.
A malicious actor is sending paycheck picture attachments via email from a forged email address, payrolldepartment@manhattan.edu. An example email is included below.
These emails are "unauthenticated" by which that means the sending SMTP (email) server is not allowed to send as any @manhattan.edu address. ITS prevents delivery of such emails to ITS managed @manhattan.edu accounts. ITS also uses DMARC to notify all receiving SMTP (email) servers to be as careful as possible with unauthenticated @manhattan.edu emails. Unfortunately, DMARC is just a suggestion and not a command. So unauthenticated @manhattan.edu emails may still be delivered to phishing targets.
From: Payroll Department
Date: Wed, Mar 1, 2023 at 1:39 PM
Subject: **PAYCHECK**
To: [redacted]
Good Day [redacted],
You are receiving this e-mail because your information has been registered and will be
scheduled for weekly payments directly from the Payroll department. The Paycheck that
covers the expenses for the office supplies you will be working with is attached in this
email. A Sales Representative will be assigned to assist you with the purchase of these
items once the funds are available from this deposit. Immediately proceed to make a mobile
deposit and contact your professor in charge once completed for clearance purposes.
Further Assignments as well as your employment documents will be sent once the supplies
are delivered. Kindly inform your professor letting him know that you have received this
email.
I have outlined Instructions on how to make a mobile deposit below.
Print out and cut it to a ( check size/shape ) At the back of your check endorse by
writing your
Full name
Mobile Deposit Only
Your account number
Sign.
Once you are done, you make a mobile deposit on your mobile banking app
Thank You.
Best Wishes,
Payroll Department.
Please do not reply to this email message. It was sent from a notification-only address
that cannot accept incoming emails.
--
Respectfully,
Office of Financial Aid Administration
4513 Manhattan College Parkway
Riverdale, NY 10471
Phone: 718-862-7100
Fax: 718-862-8027
Monday thru Friday
9:00 am to 4:30 pm
manhattan.edu/finaid
This afternoon a malicious actor, using a compromised @manhattan.edu account, sent over 2,500 phishing attempts to our organization.
If you received such a message please do not reply to it and do not follow its instructions. If you have already interacted with the malicious actor, do not do so anymore.
ITS makes use of Gmail's compliance rules (that are defined by our Google Workspace administrators) to automatically quarantine incoming or outgoing emails.
A recent phishing trend is not to use any visible text in the message body and instead use an image contained within a hyperlink that directs to a malicious login page.
Thankfully all of these phishing emails were never delivered to inboxes, spam folders, etc. They matched an existing email compliance rule and were delivered in our organization's email quarantine.
Everyday is a chance to do good. Or in the case of phishers, to do evil.
Today, ITS detected a phishing email campaign aimed at the Manhattan College community. The phishing email claims to be from the college's "Manhattan Mail Delivery Subsystem." It requests the user to click a phishing link (that displays a manhattan.edu URL but actually directs to an absolutely different domain), login with their credentials and review undelivered email messages.
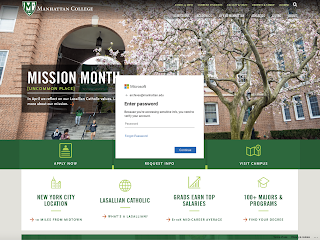 |
| Phishing login webpage that is aimed at the Manhattan College community. |
New Cyber Security Requirements
As you surely have seen in the news or in your personal life recently, cyber attacks continue to develop and increase in frequency and complexity. Many organizations - including major technology and social media companies - are taking additional steps to ensure that the accounts of their employees and customers remain well-protected. Manhattan College has not been immune to these attacks and associated risks and we are now being required to implement stricter controls for our community members who access institutional data. Given this new reality, two specific requirements that we must meet are as follows:
All Employees must complete a yearly Cyber Security training program (More information will be coming about this shortly. This must be completed by January 21st, 2022)
All Employees must enroll their JasperNet account in Multi-Factor Authentication (MFA or 2SV) (Must be enrolled by January 18th or you will be auto-enrolled)
MFA Support Sessions
ITS will be offering support sessions with members from the Technology Training team for those who will need to enable DUO Multi-Factor Authentication on their JasperNet accounts. Below please find more information about the drop-in training sessions. There is no signup required.
When:
Where: MGL 305 (Computer Lab)
Please remember to bring your cell phone to complete the setup.
If you are unable to attend or have any questions please contact its@mahattan.edu and someone from the Training Team will reach out to schedule a separate time and answer any questions you may have.
In a computer program, a logging library's purpose is to record events to a file. These events could be a request for a web page, a user reports a crash, a sensor is reporting a harmful temperature, a chatbot question from a potential consumer, etc. There is a rule in secure programming to never trust user input because the input could be constructed to subvert the program. The idea that a logging library would parse log event data is incredibly stupid and the fact that it is the default behavior of Log4j 2 until the recent version 2.15 release is the basis of the current nightmare incident we are living through.
Technology vulnerabilities are reported using the CVE (Common Vulnerabilities and Exposures) system that is maintained by The MITRE Corporation. So far, three CVEs exist due to the Log4j vulnerability and they are:
The first CVE, CVE-2021-44228, has earned a perfect ten from CVSS, which is a scoring system to measure the severity of a given vulnerability. Many security experts have jokingly wondered what a perfect ten would be given that other widely deployed software with critical vulnerabilities rarely earn a 9.8. This Log4j situation is no joke, though.
The Department of Homeland Security's Cybersecurity and Infrastructure Security Agency (CISA) has published guidance for the Log4j incident.
Additionally, CISA has established a community sourced GitHub repository.
The Apache Foundation maintains Log4j 2 and publishes the Log4j 2 Change Release History Log.
ITS is tracking the evolving nature of this situation so that our organization is not impacted. If you have any concerns about particular software, services, etc. that you use at the College please email its@manhattan.edu.
As you surely have seen in the news or in your personal life recently, cyber attacks continue to develop and increase in frequency and complexity. Many organizations - including major technology and social media companies - are taking additional steps to ensure that the accounts of their employees and customers remain well-protected. Manhattan College has not been immune to these attacks and associated risks and we are now being required to implement stricter controls for our community members who access institutional data. Given this new reality, two specific requirements that we must meet are as follows:
All Employees must complete a yearly Cyber Security training program (More information will be coming about this shortly. This must be completed by January 21, 2022)
All Employees must enroll their JasperNet account in Multi-Factor Authentication (MFA or 2SV) (Must be completed by January 18th, 2022 or you will be auto-enrolled)
Cyber Security Training
ITS is actively working with our insurance provider to develop a yearly Cyber Security training program that must be completed on a yearly basis starting in January 2022. More information about the cyber security training program will be made available in the new year and must be completed by December 31st each year. Content for the initial training program will be delivered by our insurance provider, however, we will assess the program throughout the year and provide the opportunity for campus experts to participate in determining and developing the curriculum for following years in alignment with the same requirements of the insurance provider. ALL employees (including Faculty, Graduate Assistants, and Student Employees) will be required to complete this course yearly.
Multi-Factor Authentication
Multi-Factor Authentication (MFA) - sometimes referred to as Two-Step Verification (2SV) - will be required for all employees going forward and must be implemented no later than January 2022. While Manhattan College has previously taken a very targeted and calculated approach to require MFA based on a “risk score” (i.e. users that access Banner or other escalated access), we must now require MFA for ALL employees (including Faculty, Graduate Assistants, and Student Employees). To date, over 670 community members have already enrolled in MFA. ITS will be contacting community members that still need to enroll in MFA in the coming days to provide instructions and support for enabling MFA by 1/18/2022.
MFA Support Sessions
ITS will be offering support sessions with members from the Technology Training team for those who will need to enable DUO Multi-Factor Authentication on their JasperNet accounts. Below please find more information about the drop-in training sessions. There is no signup required.
When:
Where: MGL 305 (Computer Lab)
Please remember to bring your cell phone to complete the setup.
If you are unable to attend or have any questions please contact its@mahattan.edu and someone from the Training Team will reach out to schedule a separate time and answer any questions you may have.
Today multiple gmail.com accounts sent emails to a fraction of our organization. The emails claim that the recipient would be charged $1,499 for their 12TB iCloud storage plan.
This is a good opportunity to announce that October is Cyber Security Awareness month. Best to keep in mind that any email may be a scam and we all are one degree away from criminals.
The most common IT crime still is Business Email Compromise (BEC) even though ransomware is increasing rapidly. It is best to be mindful of how to parse an email address and to do your best to understand who is emailing you.
Email addresses are formed by concatenating a username with the '@' sign and with a domain (e.g., bob@example.com). Sometimes people are confused by the common phishing addresses that use a domain inside the username (e.g., bob.manhattan.edu@example.com). Understand that such email addresses are available to anyone including to criminals.
If you receive a phishing email, you can report it to Gmail if you're using the web interface (not the Gmail mobile app, unfortunately). Google will alert ITS!
 |
| Gmail's 'Report phishing' feature is under a vertical ellipsis in the upper-right of an email. |
As we make our way into the future, the world becoming more digital by the day, it is important we are all cyber aware and understand the meaning of cyber security. In an article written by Sharon Shea, cyber security is explained to be “the protection of internet-connected systems such as hardware, software and data from cyberthreats”. Cyber security is broken up into many sections including:
Data security
Network security
Cloud security
Cyber security’s importance increases as the number of users, devices and programs continue to increase as well. This forces us to learn the threats that we are being exposed to everyday and how we can prevent them. Some threats include:
Malware
Social engineering
Phishing
By keeping up with the changing risks, we can make our own changes as simple as enabling a firewall or making complex and unique passwords for your different accounts. There are several tips you can follow including the ones in this blog post.
With our growing cyber awareness, the need for professionals in the field also grows. Cyber security comes with multiple opportunities to start a career. Some security roles include:
Security engineers
Security Architects
Security Analysts
Many other career paths are available within the field of cyber security and are in demand. The industry is in high demand for professionals who can fulfill such roles.
The growth of cyber security comes with knowledge we should all be aware of, including the risks, preventative measures, and the job opportunities it opens. Cyber security is taking on the world at an increasing pace.
Source: Shea, Sharon, et al. “What Is Cybersecurity? Everything You Need to Know.” SearchSecurity, TechTarget, 25 May 2021, searchsecurity.techtarget.com/definition/cybersecurity.