ITS will NOT ASK for you to update your password or other personal information.
As we approach the Christmas Holiday break, ITS would like to remind campus users that we will NOT be performing updates and will NOT ASK for information from you. Phishing attacks are on the rise and we are taking steps to prevent these attacks from affecting Manhattan College.
If you receive an email or other communication requesting personal information or asking you to update your password - DO NOT RESPOND. These messages should be reported to ITS or the sending office for validation.
Below are some additional resources that were previously provided to the campus community:
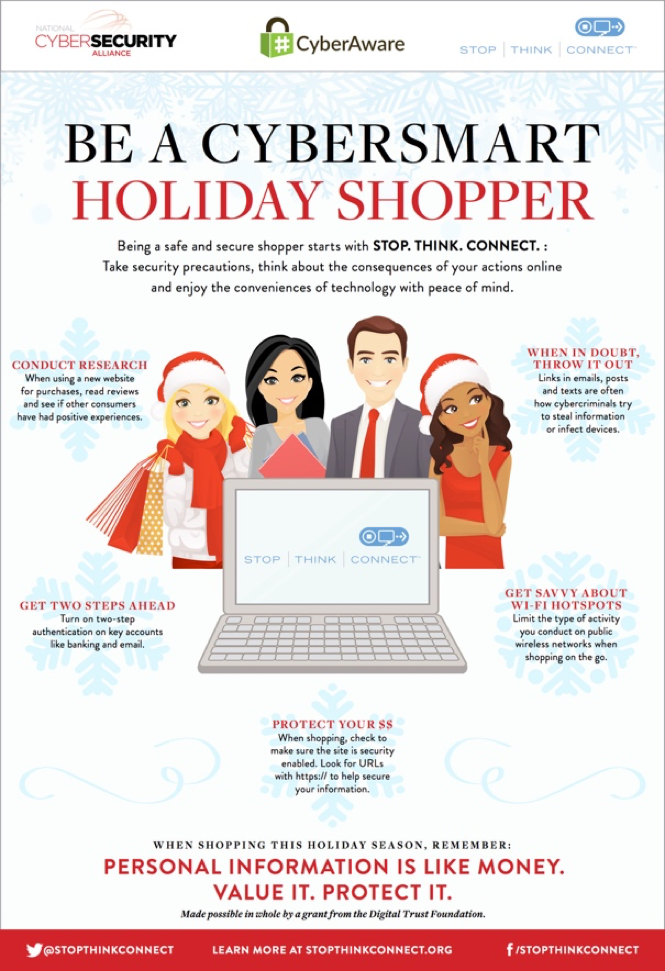
Holiday Scams and Malware Campaigns
Phishing Infographics
Half of all Phishing Sites Now Have the Padlock