Wed, 03 May 2023 17:30:03 +0000
From: MyManhattan <compromised.account@dartmouth.edu>
To: jeanbaptiste.delasalle@manhattan.edu
Subject: New Mail
Hello, You have 2 New Important Message.
LOGIN HERE TO VIEW MESSAGE DETAILS
Manhattan College
The managed-redirection URL redirects to a Japanese web server that itself is likely compromised.
So what does ITS do to mitigate this kind of attack? First our one-person information security team must concurrently do two set of actions. One set of actions is to make email compliance rules to automatically quarantine ongoing or replay phishing attacks. While the other is to label all of successfully delivered phishing emails as phishing attempts to Gmail, and then instruct Google to quarantine those emails from inboxes, spam folders, trash folders, etc. to an email administrator's email quarantine for later forensics.
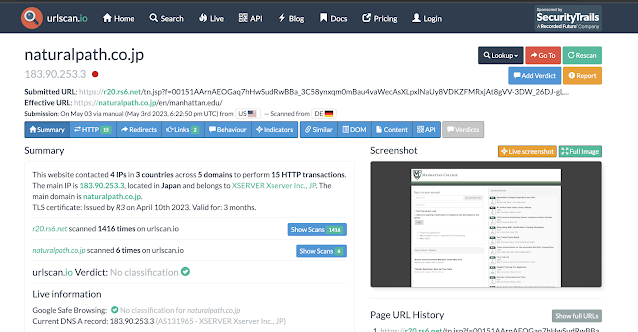 |
| Using urlscan.io, we can see that the phishing login page, shown near the bottom right, imitates the Manhattan College login page. |
So what does ITS do to mitigate this kind of attack? First our one-person information security team must concurrently do two set of actions. One set of actions is to make email compliance rules to automatically quarantine ongoing or replay phishing attacks. While the other is to label all of successfully delivered phishing emails as phishing attempts to Gmail, and then instruct Google to quarantine those emails from inboxes, spam folders, trash folders, etc. to an email administrator's email quarantine for later forensics.
That only removes the email from Gmail accounts that ITS controls. Some individuals choose to automatically forward their @manhattan.edu emails to a personal account, which is not recommended. ITS notifies all individuals who automatically forward their email to a personal account to delete the email and if they shared their credentials to change their password. All individuals who Gmail reports clicked the phishing link, are similarly notified.
Separately, Dartmouth College is notified of the compromised account and Constant Contact is notified of the malicious redirection.
But the compromised Japanese web server still exists. It is 3am in Japan so how can we promptly stop traffic to that site?
ITS notifies many Internet "police" groups. They will to help to warn (or sometimes prevent) individuals who visit the phishing site. The following is the list of Internet policing group that ITS depends upon.
In a couples months or quarters, a technology security company will blog on their past work involving hunting an Advanced Persistent Threat targeting higher education institutions and will name Manhattan College and at least two other institutions. Manhattan College's ITS and the recipients of the phishing campaign who alerted ITS played small, uncredited roles in the news reports that will follow.
 |
| Historical urlscan.io scanning reports of the compromised web server show that Manhattan College, Dartmouth College and West Virginia University have been targeted. |
 |
| Concise summary added to VirusTotal's scan. At this time, Fortinet and Trustwave are the two security vendors who are correctly labeling the phishing login site. |
Stay mindful of scams and attacks.